우리카지노: 쿠폰, 이벤트, 프로모션, 보증으로 더욱 특별하게!
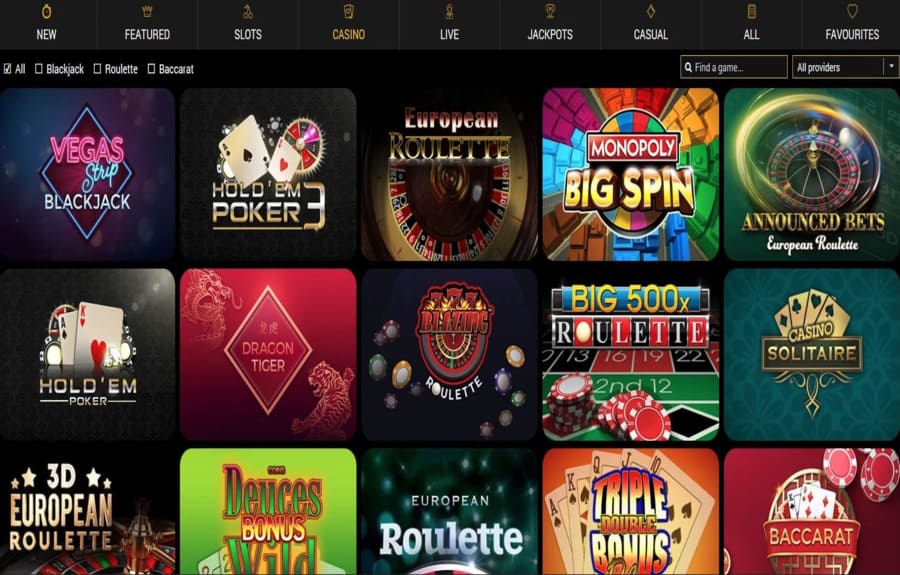
우리카지노에서 즐기는 게임은 단순한 도박 이상의 즐거움을 선사합니다. 이제 쿠폰, 이벤트, 프로모션, 그리고 보증까지 더해져 더욱 특별한 경험을 만들어줍니다. 우리카지노는 고객들에게 최고의 서비스를 제공하기 위해 끊임없이 노력하고 있습니다. 우리카지노의 다양한 이벤트와 프로모션은 많은 이용자들에게 큰 인기를 끌고 있습니다. 매주업데이트되는 다양한 혜택들로 플레이어들에게 끊임없는 즐거움을 선사하며, 게임을 더욱 재미있게 즐길 수...